You deserve security that defends liberty, not rhetoric that expands power; manufactured fear has been used to justify surveillance and erode privacy, while some leaders exploit crises for political advantage. A strong Republican form of government should prioritize limited government, accountability, and individual rights—so ask yourself: if threats are exaggerated to win votes, can policies that strip freedoms be truly protective? Understanding how fear is weaponized reveals both the danger and the opportunity to reclaim honest, principled security.
Key Takeaways:
- Fear is a political tool: leaders inflate threats to justify surveillance and power grabs — if you discovered exaggerated threats were used to win elections, would you still accept policies that strip your privacy?
- Security overreach erodes rights: emergency measures often become permanent, normalizing mass surveillance and weakening constitutional safeguards — if measures could last forever, how much freedom would future generations have?
- Truth decay fuels alarmism: sensational headlines and misinformation magnify national security scares to distract from failures and secure huge budgets, so are cyber and foreign crises being inflated to shift attention?
- Real problems, real abuse: cyberattacks, geopolitical rivals, and domestic violence are genuine threats, yet each can be exploited as cover for political advantage — ask which threats are real and which are manufactured.
- Protect the Republican form of government: a strong Republican system depends on vigilant citizens opposing fear-based centralization and defending individual liberty and local authority.
Understanding Manufactured Fear

Political actors have refined a repeatable playbook: convert a transient event into a perpetual justification for expanded authority. After the 9/11 attacks, Congress passed the USA PATRIOT Act on October 26, 2001 with overwhelming support (House 357–66, Senate 98–1), and the subsequent architecture of mass surveillance—later exposed by Edward Snowden in 2013—showed how quickly emergency measures can become enduring systems of oversight. Those developments produced mass metadata collection on millions of Americans, broader warrantless access to records, and a culture that equates visibility with safety.
Republican form of government rests on limited powers and accountable institutions, yet fear-based narratives erode those checks by normalizing permanent solutions to temporary problems. Policymakers and private contractors alike reap the benefits when budget lines swell and programs persist; the result is policy entrenchment that outlives the original threat, leaving citizens to ask: if emergency tools become standard operating procedure, who protects our liberties?
The Origins of Fear in Politics
Fear has long been a political lever—examples range from the post–World War I Red Scare and McCarthy-era purges to the 2001 security surge—where perceived external danger justified sweeping domestic measures. Campaign messaging after crises frequently shifts public priorities: in 2001 the urgency around terrorism created rapid bipartisan support for surveillance laws, demonstrating how episodic events can produce durable legal change within weeks rather than years.
Private interests and think tanks often supply the talking points that make fear persuasive, while news cycles amplify the most alarming narratives. Case studies show that when markets for security expand—contractors winning larger defense and intelligence contracts, consultants hired for emergency response—the incentive structure tilts toward perpetuating the threat frame rather than resolving it.
The Mechanics of Fearmongering
Fearmongering uses selective statistics, vivid anecdotes, and repeated framing to move audiences from concern to concession. Tactics include presenting worst-case scenarios without probability context, elevating isolated incidents into patterns, and using anonymous “intelligence” leaks as evidence. The post-9/11 environment illustrates this: isolated failures and intelligence gaps were framed as systemic collapse, producing public support for sweeping surveillance authorities that otherwise would have faced greater scrutiny.
Actors coordinating the messaging include elected officials, security contractors, aligned think tanks, and compliant media outlets; each plays a role in sealing the narrative loop that rewards alarm. Contractors such as Booz Allen—whose workforce included Edward Snowden before the 2013 disclosures—illustrate how private firms can be embedded in both operational work and policy advocacy, creating a feedback loop where policy drives profit and profit drives policy.
Specific messaging mechanics often rely on urgency cues—countdowns, predicted casualty figures, or “if we fail” framing—paired with binary choices that push the public toward acceptance of permanent trade-offs. When sunset clauses are introduced as safety valves, they are frequently extended or renewed quietly after the public’s attention moves on, converting temporary powers into lasting authorities; if you learned these renewals happen without robust debate, how would that change your view of those emergency laws?
The Role of Social Media in Amplifying Fear
Algorithms designed to maximize engagement reward emotional content, and fear is intensely engaging. A 2018 study in Science found that false news spreads significantly farther, faster, and more broadly than truth—falsehoods were about 70% more likely to be retweeted than true stories—creating an ecosystem where alarming claims gain outsized traction. Platforms magnify small incidents into national crises within hours, pressuring officials to respond in ways that expand authority.
Microtargeting and data-harvesting compounds the problem: the Cambridge Analytica scandal exposed how behavioral data from roughly 87 million Facebook users was used to tailor messaging that could stoke fear in specific groups and regions. That capability lets actors weaponize localized anxieties—crime spikes, migrant movements, cyber scares—into mobilizing narratives that change voter behavior and legislative priorities.
Bot networks, coordinated disinformation campaigns, and the economics of outrage further accelerate fear cycles; platforms’ incentive structures prefer content that prolongs attention, not content that resolves uncertainty. If social networks amplify the loudest, angriest voices, then who ensures the noise doesn’t drown out sober policy debate and the protections of a Republican form of government?
The Psychology Behind Fear
Direct neural mechanisms turn headlines into policy pressure: the amygdala flags threats faster than the prefrontal cortex can parse nuance, while stress hormones narrow attention and favor immediate action over deliberation. That physiological shortcut helps explain why Congress moved quickly after 9/11—passing the USA PATRIOT Act less than two months later—and why emotionally charged incidents repeatedly produce rapid, sweeping policy responses rather than measured solutions.
Those same shortcuts are exploitable. When fear hijacks cognition, citizens become more willing to trade privacy for promised safety, making oversight and restraint harder to demand. If you discovered that vivid images and urgent language were being used to secure permanent surveillance powers, would you still accept those trade-offs for short-term reassurance? A healthy Republican form of government relies on restrained central power and an informed public capable of resisting that pressure.
Cognitive Biases that Fuel Fear

Availability heuristic and negativity bias distort threat perception: vivid, repeated reports of attacks make rare events feel common, while loss aversion drives people to prefer avoiding potential losses over achieving gains. Public reactions to terrorism often spike after high-profile incidents even though routine risks—tens of thousands of annual traffic fatalities, for example—far outpace deaths from extremist attacks in many recent years.
Confirmation bias compounds the problem: once a narrative that “we are under siege” takes hold, people filter information that contradicts it and amplify supporting evidence. Media cycles and social algorithms accelerate this loop, helping fear-based frames reach millions rapidly and turning statistical outliers into perceived national trends that justify sweeping policy shifts.
Emotional Responses to Threats
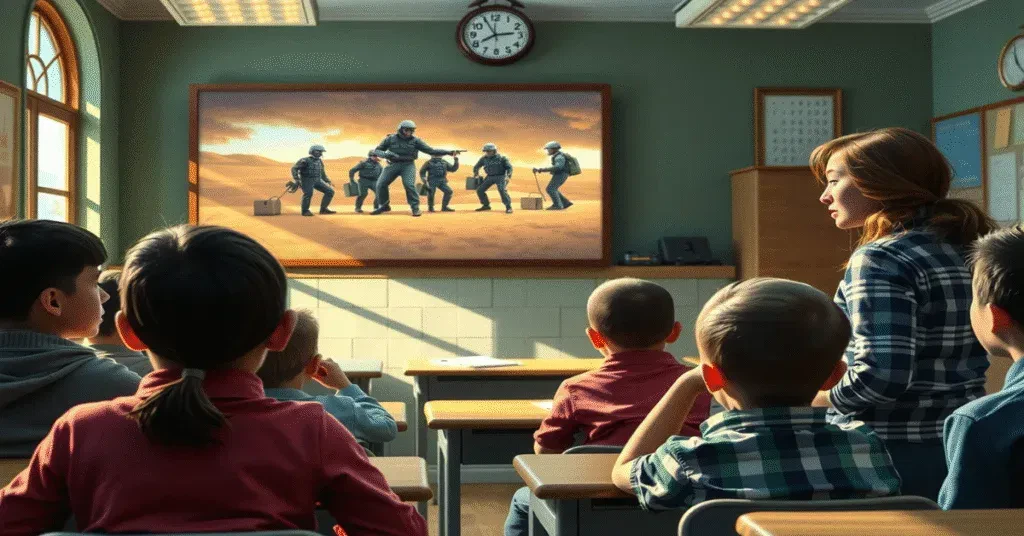
Fear triggers a cluster of emotions—anxiety, anger, disgust and protective instinct—that shape public demand for action. Political messaging that foregrounds children, homeland imagery or visceral scenes converts generalized concern into targeted support for specific policies; appeals that provoke protective instincts can increase backing for surveillance, detention powers, or expanded executive authority.
Anger, in particular, simplifies attribution and punishment: when an enemy is identified, support for punitive measures rises sharply. That emotional trajectory helps explain why fear-based campaigns frequently produce policy wins even without robust evidentiary bases—emotion overrides cost-benefit reasoning and compresses debate.
Physiological stress amplifies these effects: acute stress increases preference for decisive leadership and punitive solutions, making voters more receptive to promises of strong, immediate action. That dynamic both empowers leaders who wield fear and weakens the institutional checks that protect civil liberties.
Fear Conditioning and Political Compliance
Repeated pairing of a cue (threat alerts, nightly terror headlines) with a policy outcome (surveillance, emergency powers) creates conditioned compliance over time. The Homeland Security color-coded alerts and other symbolic signals served as public Pavlovian cues—each elevation reinforced the association between perceived threat and acceptance of expanded state authority. This process is a form of fear conditioning that can make temporary measures feel permanent.
Institutional factors deepen the effect: emergency powers fast-tracked in crisis are often reauthorized or normalized, and oversight mechanisms weaken under continuous threat narratives. FISC approval rates approaching 99% for surveillance requests and the steady expansion of surveillance authorities after 2001 illustrate how legal and technical systems can lock in compliance once conditioned responses take hold. If alerts and rhetoric trained citizens to accept intrusions as the price of safety, would rollback become politically feasible?
Longer-term consequences include policy lock-in—budgets swelling into the tens of billions annually for homeland and intelligence programs, vendor ecosystems profiting from surveillance, and public expectation that security equates to constant monitoring. That institutional momentum makes it harder to restore the balance between liberty and security that a Republican form of government must preserve.
Case Studies of Political Fearmongering
Several high-profile events show how fear becomes policy fuel: emergency rhetoric fast-tracks laws, enlarges budgets, and normalizes oversight-free programs that persist long after the moment passes. Examples below pair the headline narratives with concrete numbers—casualties, budgets, affected populations—to reveal what was real, what was amplified, and who benefited from the resulting powers.
Those outcomes matter to the future of a Republican form of government: emergency measures enacted under popular duress shape institutions for decades. If evidence later shows the threat was overstated, would you accept permanent changes to surveillance and executive authority? The case studies that follow trace the pattern.
- 9/11 & Patriot Act (2001) — 2,977 people killed on September 11, 2001; USA PATRIOT Act passed on October 26, 2001; Department of Homeland Security created in 2002 consolidating ~22 agencies; sweeping expansions of surveillance and information-sharing authorized.
- Iraq War & WMD (2003) — 2003 invasion based on intelligence assessments claiming active WMD programs; post-invasion inspections found no stockpiles; U.S. military deaths numbered in the low thousands and overall cost estimates exceed $1.5–$2 trillion when long-term obligations are included.
- NSA Programs & FISA Expansions — warrantless collection and bulk metadata programs revealed in the 2000s and again in 2013; public disclosures led to legal challenges and limited reforms, while some surveillance authorities remained in place under revised rules.
- Equifax & Consumer Data Breach (2017) — breach exposed personal data of approximately 147 million Americans; used as justification for calls to centralize ID databases and strengthen industry surveillance measures.
- SolarWinds & Supply-Chain Compromise (2020) — malware inserted into updates used by roughly 18,000 customers, including federal agencies; spurred emergency directives and increased cybersecurity contracting and budget requests.
- Ransomware Incidents (2020–2021) — Colonial Pipeline shutdown (May 2021) led to temporary fuel shortages; Colonial paid roughly $4.4 million ransom (partially recovered later); episodes used to argue for broader authorities and funding for offensive cyber operations.
The 9/11 Attacks and Its Aftermath
Official and public reaction after September 11 produced immediate institutional change: the USA PATRIOT Act broadened surveillance authorities, and creation of the Department of Homeland Security centralized responsibilities previously spread across agencies. Lawmakers justified rapid transfer of powers with live images of catastrophe and a casualty figure—2,977 dead—that left little appetite for slow deliberation.
Those new authorities translated into enduring programs: sections of the Patriot Act expanded roving wiretaps, business record orders, and intelligence-sharing that prosecutors and intelligence agencies still cite today. If you examine the timeline, emergency adoption of these measures set precedents for future crises—do temporary powers really always expire when the emergency narrative fades?
The Iraqi War and Weapons of Mass Destruction

Claims that Iraq possessed active WMD programs were central to the 2003 justification for military intervention. A 2002 National Intelligence Estimate and public speeches framed the issue as an imminent danger. After invasion, multinational inspections failed to locate the alleged stockpiles, and major post-war assessments concluded key intelligence judgments were mistaken or overstated.
Policy consequences were significant and long-lasting: costs measured in the low trillions of dollars when lifetime veteran care and interest are included, more than 4,000 U.S. military fatalities in early years of conflict, and broad regional destabilization. Those outcomes reshaped public trust and foreign policy priorities for years.
Further detail: congressional and independent inquiries—among them the Senate Intelligence Committee reviews—documented analytic failures, stovepiped reports, and politicized language that amplified uncertainty into certainty. If political leaders can convert equivocal intelligence into a decisive call for war, what guardrails should a Republican form of government demand before giving away the power to act?
The Rise of Cyber Threat Warnings
Since the mid-2010s, high-profile breaches and supply-chain attacks have driven a steady escalation in rhetoric about cyber catastrophe. Incidents like the 2017 Equifax breach (about 147 million consumers affected), the 2020 SolarWinds compromise (software used by roughly 18,000 customers), and high-impact ransomware events have been presented as proof that extraordinary authorities and funding are necessary.
That narrative produced a surge in federal contracts, emergency directives, and proposals for increased surveillance and offensive cyber capabilities, often justified with projected cost figures and worst-case scenarios. Global and federal cybersecurity budgets ballooned as agencies and contractors positioned themselves as the solution—how much of that spending prevented harm, and how much was driven by the politics of fear?
More information: ransomware payments and business disruption figures—Colonial Pipeline’s roughly $4.4 million ransom, for example—are used to argue for expanded authorities and collaboration between government and private sector. Yet public policy responses sometimes prioritize centralized control and funding flows over measured resilience improvements that protect civil liberties under a Republican form of government.
Security Theater: An Illusion of Safety
Security theater substitutes the appearance of protection for actual effectiveness, trading measurable outcomes for visible gestures that assuage fear. From theater-level airport rituals—shoe removal, liquid limits, intrusive pat-downs—to high-profile police checkpoints, these actions generate headlines and a sense of action while often producing no measurable reduction in threat.
Political actors exploit that mismatch: visible steps are easier to sell to voters than complex, less-visible investments like intelligence fusion, counterintelligence, or infrastructure hardening. That tradeoff channels taxpayer dollars into optics, expands surveillance, and normalizes permanent powers under the guise of temporary fixes—outcomes that undermine a healthy Republican form of government built on limited powers and accountable oversight.
Understanding Security Theater
Security theater works because humans respond to signals; a metal detector, a uniformed guard, or a national alert reassures the public even if the measure itself has weak efficacy. Academic reviews and oversight reports have repeatedly shown that highly visible controls often have low hit rates for preventing sophisticated threats, while intelligence-led approaches that cost less politically tend to perform better.
Concrete examples tie this concept to policy: after 9/11 the Patriot Act broadened surveillance authorities, and Edward Snowden’s 2013 disclosures exposed bulk collection programs that prioritized volume over actionable leads. Those programs produced few publicized disruptions of attacks yet delivered extensive erosion of privacy, prompting reforms like the USA FREEDOM Act in 2015 to curb indiscriminate metadata collection.
Examples of Ineffective Security Measures
Air travel rules that change frequently—laptop removals, 3.4-ounce liquid limits, routine pat-downs—offer the illusion of control while adversaries adapt around predictable checks. Mass CCTV deployment and visible patrols often fail to stop premeditated plots; surveillance yields thousands of hours of footage with few preventative interventions, creating a resource drain more than a deterrent.
Bulk data collection and dragnet surveillance are particularly pernicious: they collect millions of records for minimal actionable intelligence, exposing citizens to long-term privacy harms and mission creep. Visible campaigns like “random” checkpoints at highways produce headlines but rarely yield sustained disruption of organized threats, illustrating how theater reallocates attention away from targeted investigations.
Case in point: wholesale metadata programs justified broad collection under Section 215 of the PATRIOT Act until legal and public pressure led to the USA FREEDOM Act’s 2015 reforms, demonstrating that sweeping, visible programs can be both costly and legally unsustainable when evidence of effectiveness is thin.
The Impact on Public Trust
When citizens perceive security as performance rather than protection, trust in institutions erodes; cooperation drops, reporting of suspicious activity declines, and public resilience weakens. Polling and watchdog findings over recent decades show falling confidence in government handling of security and privacy, a dynamic that empowers those who would expand power under the pretext of safety.
A strong Republican form of government depends on informed consent and oversight; security theater corrodes both by normalizing unchecked authority and by training the public to accept invasive measures as inevitable. Once trust is lost, legitimate policies—targeted surveillance with warrants, community-based prevention, hardened infrastructure—face skepticism that hobbles effective defense.
Erosion of trust has practical consequences: lower reporting rates, reduced intelligence-sharing from communities, and political polarization that makes bipartisan oversight harder to achieve—outcomes that increase long-term vulnerability even as short-term optics improve.
The Media’s Role in the Fear Economy
Sensationalism and Clickbait Headlines
Newsrooms and platform-driven publishers optimize headlines to maximize clicks and shares; outlets openly A/B test language because emotion-laden headlines produce measurable lifts in engagement. Advertising dollars follow attention—U.S. digital ad spending topped $200 billion in the early 2020s—so headlines that provoke fear translate directly into revenue, incentivizing repeated use of alarmist framing.
Coverage after major events shows how quickly sensational headlines can reshape policy: widespread, sustained reporting on terrorism after 9/11 helped create the public mandate that allowed the Patriot Act to become law just 45 days later. A pattern emerges where attention-seeking copy converts fear into political capital and permanent policy shifts.
The 24/7 News Cycle and Fear Propagation
Round-the-clock cable channels and algorithmic social feeds create a feedback loop in which the same alarming images and talking points are replayed endlessly, increasing perceived threat regardless of underlying data. CNN’s 24-hour model (launched in 1980) combined with social platforms’ engagement algorithms means stories that trigger outrage or anxiety get amplified at scale; internal platform research and industry reporting have repeatedly shown that content evoking anger or moral outrage generates above-average spread.
Continuous exposure changes public risk perception: Americans still spend roughly four hours a day on TV and video, and repeated fearful frames make rare events feel common. Algorithms that prioritize engagement can turn isolated incidents into national crises, pressuring elected officials to act on perception rather than evidence—does that serve the public, or power?
More info: An MIT study of Twitter diffusion found falsehoods spread farther and faster than true stories, with true stories taking about six times longer to reach 1,000 people than false ones; that dynamic means the 24/7 cycle doesn’t merely report fear, it accelerates misinformation and magnifies unverified claims into policy drivers.
Documenting Dangers vs. Creating Them
Investigative reporting that exposes real vulnerabilities performs a public good—Edward Snowden’s disclosures in 2013, for example, revealed extensive NSA programs and helped spur the USA FREEDOM Act (2015), which limited certain bulk collection practices. Responsible journalism surfaces evidence, forces oversight, and produces corrective legislation; the contrast with sensational coverage is stark when reporting substitutes drama for documentation.
Conversely, media amplification of uncertain intelligence has produced disastrous outcomes: coverage of alleged WMDs in Iraq in 2002–2003 demonstrated how repeated, unvetted claims can manufacture consent for major policy moves. A healthy Republican form of government depends on sober information and institutional checks, not headlines engineered to elicit panic.
More info: Assessing reportage requires asking specific questions about sources, corroboration, and motive—who benefits from this narrative, what is the evidence, and how quickly are policy prescriptions following the coverage? If the answer points to rushed claims and immediate calls for expanded powers, the line between documenting a danger and creating one has likely been crossed.
The Financial Incentives Behind Fear
Billions flow through the national security apparatus each year, and those dollars shape policy as much as intelligence does. Federal discretionary defense spending has stayed in the hundreds of billions annually, while high-profile programs like the F-35 carry estimated lifecycle costs north of $1.7 trillion, creating powerful incentives to justify continued investment. If you discovered that threat narratives directly correlate with budget increases and multiyear contracts, would you still accept every new alarm at face value?
Private and public actors both benefit when perceived danger rises: contractors win contracts, consultants bill for risk assessments, and media outlets monetize attention spikes. That dynamic erodes the Republican form of government’s principles of limited federal power and local accountability by making centralized, permanent funding the default response to episodic scares.
The Military-Industrial Complex

President Eisenhower warned about the military-industrial complex for a reason: long-term procurement and a revolving door between the Pentagon and industry create structural momentum toward more spending. Major defense contractors—whose annual revenues run in the tens of billions—depend on program continuity; canceling a program like the F-35 or other major platforms threatens thousands of jobs and supply-chain contracts across congressional districts, which in turn pressures legislators to sustain budgets and justify new threats.
Lobbying and personnel movement amplify that pressure. Former DoD officials often join defense firms, bringing insider knowledge and relationships that translate into preferential access during procurement decisions. Ask yourself: when top contractors and Pentagon alumni jointly push a threat narrative, whose interests are being defended—the public’s, or the balance sheets that pay for campaign contributions and influence?
Fear-based Lobbying and Political Funding
Security-focused PACs and corporate political spending spike around high-profile incidents, and the industry funnels millions into campaigns and lobbying each cycle to lock in policy outcomes. Open-source tallies show the broader security industry regularly invests tens to hundreds of millions annually in lobbying; that cash buys staff time, committee access, and legislative language that favors sustained program funding over targeted, evidence-based responses.
Grants and earmarks tied to homeland security or defense often land in districts with well-connected firms, rewarding political actors who advocate for larger budgets. When local economies become dependent on federal security contracts, elected officials face a strong incentive to endorse fear-forward policies that keep the money flowing—and voters rarely see the trade-offs behind closed-door negotiations.
Detailed case studies illustrate the pattern: after 9/11, homeland security grant formulas and Department of Defense contracting shifted in ways that benefited states and districts with preexisting defense infrastructure, while the growth in earmarks and classified contracting obscured cost-benefit analysis. How would policy change if funding decisions were driven by independent risk assessments instead of political patronage?
The Profit Motive of Private Security Firms
The private security sector—from armored-vehicle firms to boutique cyber vendors—is a multi-billion-dollar market that expands as perceived risk rises. Contracting for physical protection, intelligence analysis, and incident response became a permanent industry after major crises; private firms now sell services that once fell solely to public institutions, and their revenue models reward alarmed clients willing to pay for constant vigilance.
Notorious incidents expose the dangers of outsourcing force and intelligence to profit-driven entities. The 2007 Baghdad Nisour Square killings involving a U.S. private security contractor highlighted how privatized security can produce accountability gaps and escalate violence, creating new security problems that then justify more contracts and oversight mechanisms that never fully restore public trust.
Private cybersecurity firms follow a similar loop: selling vulnerability assessments, threat alerts, and remediation packages generates recurring revenue whenever threats are amplified. When vendors and public agencies rely on each other to define “emergency,” the system risks turning intermittent threats into permanent markets—who benefits when alerts are calibrated to sustain sales rather than to stop concrete attacks?
The Erosion of Civil Liberties

The Balancing Act Between Security and Freedom
After 9/11, the Patriot Act (Oct 26, 2001) and post‑9/11 programs shifted the baseline: what began as targeted tools expanded into routine practices. Snowden’s 2013 disclosures exposed programs like PRISM and bulk telephone metadata collection that were justified as necessary for counterterrorism; Congress later curtailed the worst excesses when the USA FREEDOM Act (2015) ended some forms of bulk collection, but targeted authorities such as FISA Section 702 remain in force. That history shows how quickly emergency measures become permanent fixtures unless constrained by law and oversight.
Local and state programs tell the same story: by the early 2010s more than 70 fusion centers were operating across the country, aggregating data from police, private contractors, and federal agencies and normalizing surveillance at every level. A healthy Republican form of government rests on limited, accountable federal power; ask yourself—if security arguments systematically shift authority away from elected local officials and towards unaccountable agencies, who is actually being protected?
Legal Ramifications of Overreach
Warrantless or minimally‑regulated surveillance erodes the Fourth Amendment’s protections against unreasonable searches. Key legal fights illustrate the stakes: ACLU v. Clapper (2015) produced a Second Circuit opinion that found the NSA’s bulk metadata program unlawful, yet the case underscored standing and secrecy problems that left many practices untouched. Secretive proceedings in the Foreign Intelligence Surveillance Court (FISC) make ex post oversight difficult, and legal doctrines like minimized disclosure and in camera review limit public scrutiny of how authorities interpret broad statutes.
Overreach also has chilling effects on speech and association: targeted monitoring of journalists, activists, and political opponents—even when carried out under national security authorities—can suppress dissent and distort public debate. Litigation trends show civil liberties groups filing more suits and FOIA requests, but successful remedies are often slow; statutory reforms and clearer judicial standards remain necessary to restore balance between legitimate threats and constitutional rights.
More specifically, the combination of high approval rates in secret court proceedings and broad statutory language gives agencies leverage to interpret terms like “relevant” or “foreign intelligence” expansively; that interpretive room has produced collection practices not envisioned by the statutes’ drafters. If legal guarantees are to mean anything in practice, Congress must tighten definitions, increase adversarial review in FISC proceedings, and require transparent reporting on the scope and use of collected data.
Historical Context of Civil Liberties under Threat
History provides stark precedents for how fear reshapes rights: the 1944 Korematsu decision upheld Japanese internment during wartime and was formally repudiated by the Supreme Court in Trump v. Hawaii (2018), a rare judicial admission that constitutional deference to executive security claims can produce grave injustice. The internment example shows how security rationales can override property, liberty, and citizenship in ways that take generations to correct.
Post‑9/11 responses followed a familiar arc: rapid expansion of authority, normalization through routine practice, then piecemeal reform after public exposure. The Patriot Act, expanded TSA powers, and the creation of new intelligence sharing networks mirror earlier episodes—suggesting a pattern where episodic crises reshape long‑term legal norms unless actively checked by citizens and their representatives.
Deeper study of these periods reveals repeatable mechanics: surveillance tools deployed for a specific threat diffuse into general policing and intelligence activities, oversight bodies struggle to keep pace, and legal doctrine often lags technological change. Those dynamics explain why a Republican form of government that emphasizes limited federal reach and robust individual rights is imperative to prevent temporary measures from becoming permanent erosions of liberty.
The Surveillance State and Its Implications
Post-9/11 expansions—most notably the Patriot Act’s Section 215 and the NSA programs exposed by Edward Snowden in 2013—shifted surveillance from targeted investigations to routine mass collection of communications metadata and internet traffic. Reforms like the USA FREEDOM Act of 2015 narrowed one pathway for bulk collection, but intelligence budgets now exceed tens of billions annually and technological capability has outpaced oversight, leaving vast troves of personal data vulnerable to mission creep and political misuse.
Unchecked surveillance corrodes the republican form of government by concentrating information and power in executive agencies rather than with accountable representatives. Ask yourself: if officials can track political organizers, journalists, and ordinary voters in real time, who then holds those officials accountable? The balance between security and liberty tilts when secrecy is justified by vague threat narratives that rarely face independent scrutiny.
Mass Surveillance Programs
The NSA’s PRISM and XKeyscore revelations showed direct collection from major tech platforms and the ability to search global communications, while domestic tools proliferated through FBI programs and local fusion centers—about 80 fusion centers were set up to share intelligence between federal and state actors. Programs using National Security Letters and expansive interpretive authorities enabled agencies to obtain phone, financial, and transactional metadata without traditional court oversight, creating a parallel intelligence system that often operates outside public view.
Private-sector partnerships amplified state reach: telecom carriers, cloud providers, and data brokers became conduits for government access, whether by legal compulsion or undisclosed agreements. The result: systemic data aggregation—from call logs to ride-share histories—makes it trivial to reconstruct individuals’ associations and movements, and that capability can be weaponized in political campaigns or law enforcement priorities that mirror partisan aims.
The Role of Technology in Monitoring Citizens
Modern surveillance relies on tools that turn everyday devices into trackers: smartphone location feeds sold by app ad networks, license-plate readers that catalog comings and goings, and IMSI catchers (“Stingrays”) that mimic cell towers to harvest device identifiers. Facial recognition moved from labs into law enforcement workflows; in 2018 the ACLU’s test falsely matched 28 members of Congress using Amazon’s Rekognition, highlighting bias and wrongful identification risks for minorities and critics of power.
Commercial actors intensified reach—Clearview AI scraped over three billion images from the web to build a searchable face database for police, sparking lawsuits and regulatory scrutiny. Predictive policing platforms, trained on historical data, often replicate and amplify past enforcement biases, funneling communities into cycles of surveillance and arrest that benefit no one except those who profit from inflated threat metrics and enforcement contracts.
Technical fixes alone won’t solve the problem: governance must limit indiscriminate collection, enforce retention limits, and require ex ante judicial review for novel sensor deployments. Would you accept unregulated facial recognition scanning at public gatherings if that power could later be used to chill political speech or target opposition in an election year?
Public Reaction and Backlash
Civic resistance translated into concrete policy wins: San Francisco banned municipal use of facial recognition in 2019, and numerous city councils followed with restrictions or moratoria on biometric surveillance—demonstrating that local governance can push back against overreach. Litigation under Illinois’ BIPA and other privacy statutes produced high-profile settlements, including a roughly $650 million settlement tied to photo-tagging practices that forced companies to reconsider biometric defaults.
Grassroots organizing, tech-worker protests (for example, employee pushback against defense contracts), and civil liberties lawsuits have pressured vendors and agencies to pause or curtail deployments. Public outrage often centers on data broker practices and hidden location-tracking: revelations that app data sold to contractors can place individuals at protests, clinics, or political events make the trade-off between convenience and freedom palpably evident.
Policy momentum favors stronger safeguards when citizens demand transparency and elected officials answer: will your representatives defend a republican form of government by imposing strict oversight, or will they trade accountability for the short-term political advantages that fear and opaque surveillance provide?
Psychological Warfare and Public Manipulation
Framing and repetition have replaced debate in many high-stakes security conversations: selective leaks, timed briefings, and graphic imagery convert complex threats into simple, urgent narratives that demand immediate action. Edward Snowden’s 2013 revelations about NSA programs like PRISM and XKeyscore exposed how information control can be paired with legal authority—Section 215 of the Patriot Act was cited for bulk collection until the 2015 USA FREEDOM Act curtailed some of those powers—showing how quickly extraordinary measures can become permanent policy tools. A healthy republican form of government depends on informed consent, not manufactured panic.
Techniques Used in Psychological Manipulation
Fear-based messaging leverages cognitive shortcuts: the availability heuristic (salient incidents presented as common), emotionally charged anecdotes over statistics, and constant repetition across TV, social media, and op-eds. Campaigns deploy targeted microadvertising and data-driven segmentation—recall Cambridge Analytica’s role in 2016-style microtargeting—to tailor threat narratives to specific voter cohorts, increasing perceived risk without changing underlying probabilities.
Official channels and allied think tanks often use selective intelligence releases, unnamed-source briefings, and red-team scenarios to create a sense of imminent danger; staged “leaks” and exaggerated casualty projections are common. Combining these with visual terror cues and loaded language produces rapid public pressure for policy shifts—more surveillance funding, fewer legal safeguards, and emergency authorities that are rarely rolled back.
Effects of Fear on Public Opinion
Fear skews risk perception: isolated incidents become policy drivers when amplified. After 9/11, public support for sweeping surveillance and expanded executive power surged; once institutions adapted—budgets increased and technologies deployed—reversal proved difficult. Polling patterns historically show large spikes in support for restrictive measures in the weeks following high-profile attacks or crises, translating into legislative windows where civil liberties are traded for promised security.
Polarization intensifies as fear feeds identity politics and scapegoating, making compromise politically costly. Media outlets that profit from sensational headlines accelerate this process, and partisan actors exploit it to consolidate power. If you discovered that exaggerated threats were being used to win elections, would you still accept policies that permanently expand state reach?
Additional evidence shows institutional inertia: intelligence agencies and contractors expand capabilities during emergencies and then lobby to preserve budgets and authorities. The result is a feedback loop—fear creates power gains, power manufactures new fears—which hardens public opinion in favor of permanent security measures even after the initial threat recedes.
The Long-term Consequences of Fear-based Governance
Normalization of emergency authorities erodes legal safeguards over time: temporary surveillance authorities can become routine, judicial oversight weakens, and precedent makes future expansions easier. Internationally, other states cite U.S. practices to justify their own crackdowns, while domestically the private surveillance sector grows into a multi-billion-dollar industry with vested interests in maintaining threat narratives.
Trust in public institutions declines as citizens learn that some threats were exaggerated for political ends; that decline fuels cynicism and disengagement, undermining the very consent needed for a functioning republican system. Generational memory shifts too—young people raised under perpetual security paradigms accept diminished privacy and stronger state power as normal rather than exceptional.
More detail: bureaucracies built around fear lock in budgets, expertise, and regulatory capture—contractors and agencies create career incentives to perpetuate perceived threats—so rolling back powers requires both legal reform and a public willingness to confront how fear was manufactured in the first place.
Fear, Distrust, and Social Division
How Fear Breeds Distrust Among Citizens
Patriot Act provisions like Section 215 and the 2013 Snowden disclosures about NSA bulk collection transformed abstract security policy into a lived experience for millions, producing widespread suspicion that private communications and everyday movements are monitored. Communities targeted by aggressive policing or surveillance—Muslim neighborhoods after 9/11, low‑income neighborhoods subject to stop‑and‑frisk—report lower cooperation with authorities, fewer tips to police, and a retreat from civic life as people fear being profiled or swept into investigations.
Legislative responses such as the USA FREEDOM Act of 2015 rolled back portions of bulk collection, but the lasting effect has been damage to public trust: oversight cycles reveal how quickly emergency powers expand and persist. If you discovered that exaggerated threats were being used to win elections, would you still trust the policies that strip away privacy and neighborly trust? The answer determines whether oversight and civic cooperation can be rebuilt.
The Impact on Community Cohesion
Neighborhoods fracture when suspicion replaces solidarity: parents stop letting children play outside, local meetings draw fewer participants, and immigrant communities avoid public institutions for fear of exposure to enforcement. The stop‑and‑frisk era in New York (rising in the 2000s and legally challenged in Floyd v. City of New York, 2013) provides a clear case study of how aggressive security tactics can erode relationships between residents and the state, leaving long‑term scars on social capital.
Fear‑driven misinformation compounds that erosion—Pizzagate in 2016 culminated in an armed intrusion at Comet Ping Pong, showing how conspiratorial narratives can turn rumor into real‑world danger and further fray community bonds. Local businesses, houses of worship, and schools become defensive spaces, reducing informal networks that once mediated conflict and supported resilience.
Economic and civic costs follow: volunteerism dips, turnout at town meetings falls, and businesses avoid neighborhoods seen as risky, all of which weaken the strength of a Republican form of government that depends on active, locally rooted citizen participation rather than centralized coercion.
Polarization in Political Discourse
Fear rhetoric converts policy debates into existential fights: opponents are framed not as rivals but as threats to survival, which eliminates room for compromise and primes supporters for confrontation. The information ecosystem accelerates this trend—an MIT study (2018) showed falsehoods spread farther and faster than truth on social platforms—so alarmist narratives gain traction overnight and become entrenched talking points across media.
Events like the January 6, 2021 attack on the Capitol illustrate how sustained fear narratives and coordinated misinformation can produce political violence and institutional trauma, eroding the norms that allow a Republican form of government to function through local institutions and law. Security budgets expand and emergency authorities are granted with less scrutiny when public debate is dominated by polarized, fear‑infused messaging.
Longer term, polarization hardens policy positions and makes oversight rare: Congress moves from deliberation to performance, media outlets prioritize outrage for engagement, and citizens sort into informational silos. If threats are being amplified to win votes, would you still accept permanent powers that bypass local accountability and reshape civic life? That question matters more than ever.
Overcoming the Culture of Fear
After the Snowden revelations in 2013 and the passage of the Patriot Act’s Section 215, public pushback produced the USA Freedom Act of 2015, which curtailed bulk phone metadata collection—proof that policy can be rolled back when citizens demand evidence over alarm. Restoring balance means more than repeals: it requires institutional changes such as mandatory sunset clauses on emergency authorities, routine independent audits of surveillance programs, and transparent budget line-items so the public sees whether billions are spent on real risk reduction or political theater.
Defending a republican form of government depends on rebuilding civic competence and oversight so fear cannot be monetized into permanent power. If you discovered that exaggerated threats were being used to win elections, would you still accept indefinite surveillance powers cast as emergencies? Concrete remedies—tightened standards for intelligence claims presented to Congress, whistleblower protections with rapid adjudication, and statutory limits on data retention—turn that question from hypothetical into policy.
The Importance of Critical Thinking
Case studies show how sloppy reasoning lets fear flourish: post-9/11 rhetoric justified Section 215 by treating isolated incidents as systemic collapse, and later NSA programs were revealed to collect far more metadata than the public expected. Training citizens to interrogate claims—asking for primary sources, timelines, and measurable outcomes—exposes when a threat narrative lacks evidence. Fact-based scrutiny forced legislative change in 2015; similar scrutiny can force transparency around cybersecurity budgets and emergency declarations.
Practical steps include integrating source-evaluation exercises into high school civics, funding public-interest journalism that traces government claims to original documents, and supporting watchdog NGOs that use FOIA and impact litigation—organizations like the ACLU and EFF have repeatedly turned opaque security claims into testable court records. If policymakers must answer to a population that can parse evidence, then fear loses its leverage.
Media Literacy as a Tool Against Manipulation
Weaponized headlines thrive when readers accept emotional framing instead of evidence. Techniques such as reverse-image searches, domain checks, and cross-referencing claims against primary sources blunt the effect of sensational security stories. During major events—election cycles and public-health crises—fact-checkers like PolitiFact, Snopes, and FactCheck.org have repeatedly corrected viral falsehoods; amplifying those corrections through libraries and schools reduces reach of weaponized headlines.
Programs in countries like Finland show measurable gains: national curricula that teach source verification and bias recognition correlate with lower susceptibility to misinformation. Implementing similar curricula and funding community workshops and public library training sessions can shift the information environment from panic-ready to verification-driven. Would you rather accept a fearful headline—or require corroboration before policy follows?
Simple, scalable tools speed this work: browser extensions like NewsGuard, reverse-image engines such as TinEye and Google Images, and centralized verification hubs in local newsrooms cut the time needed to vet claims. Tech platforms can also publish transparency reports that list the provenance of trending security stories, making it easier for citizens and legislators to spot manufactured crises before they calcify into law.
Building Resilience in Society
Local institutions offer friction against top-down fearmongering: city councils, state legislatures, and school boards can require impact assessments before adopting surveillance tech, and mandate yearly independent audits. A concrete model is requiring any surveillance program to include a one- or two-year sunset review and public cost-benefit disclosures—steps that turned the tide on several municipal facial-recognition pilots in recent years.
Civic resilience also rests on channels for accountability: empowered inspector generals, accessible FOIA processes with strict response timelines, and publicly funded investigative journalism. When whistleblower disclosures triggered congressional hearings in 2013, oversight followed; institutionalizing those pathways prevents manipulation from becoming permanent. How long would you let an emergency law remain if no one could test its claims?
Actionable policy items include mandatory annual audits published in plain language, statutory limits on data retention tied to the specific threat addressed, and requirement that any new national-security budget line be justified with measurable objectives and independent risk assessments. Those reforms make fear harder to weaponize and make governing under a republican form of government responsive rather than reactive.
Reclaiming Agency and Liberty
Grassroots pressure, legal pushback, and technological choices together can reverse the momentum that turned fear into policy. Victories like the 2015 USA FREEDOM Act, which curtailed bulk phone-record collection under Section 215, and municipal bans on facial-recognition systems (San Francisco led the way in 2019) show that coordinated action produces concrete rollbacks of invasive practices. Citizens who adopt strong privacy tools—end-to-end encrypted messaging, burner accounts for risky interactions, and routinely auditing app permissions—reduce the leverage that fear-based surveillance relies on.
Republican principles of limited government and separation of powers provide a framework for reclaiming authority from centralized security bureaucracies: insist on sunset clauses, independent audits, and local control rather than open-ended federal grants of power. Small, sustained campaigns at the state and county level have repeatedly forced federal policies to be examined and in some cases rescinded; what if more Americans treated privacy protections as a practical extension of those principles?
Grassroots Movements Against Fearmongering
Post-2013 organizing around the Snowden revelations crystallized into national and local campaigns—groups like the ACLU and EFF filed lawsuits, while citizen-led protests such as Restore the Fourth mobilized volunteers in dozens of cities to demand limits on surveillance. Legal pressure and public demonstrations contributed directly to legislative changes and to private-sector adjustments: after public outcry, several major tech firms strengthened encryption defaults and began publishing detailed transparency reports on government data requests.
State-level activism has been especially effective at the ballot-box and council level: California’s privacy law (CCPA) in 2018 and municipal bans on law-enforcement use of facial recognition show that targeted local campaigns can produce measurable policy shifts. Would you rather fight for fixes in Washington or win protections where you live and vote?
Political Accountability and Transparency
Oversight mechanisms—congressional hearings, Inspector General audits, and Freedom of Information processes—work when they are funded and used. The 2014–2015 oversight cycle, which included high-profile hearings on NSA programs and IG reports, produced policy changes because lawmakers faced sustained public pressure and media scrutiny. Require agencies to publish periodic impact assessments and raw data where possible so citizens and watchdogs can quantify harms and costs; sunset provisions force re-evaluation rather than perpetual expansion of authority.
Whistleblower channels and legal protections matter: the Snowden disclosures exposed practices that internal reports had failed to correct. Strengthening safe, legal reporting routes for federal employees and contractors reduces the need for leaks while preserving accountability. Ask yourself—do you trust opaque bureaucracies or institutions that must explain and justify their actions openly to elected representatives under a Republican form of government?
More transparency comes from demanding that technology companies publish granular transparency reports (Google, Apple, and Microsoft already release counts of requests for user data) and from pushing Congress to require metadata-level disclosures about surveillance program scope. Funding for Inspectors General and GAO audits should be nonpartisan line items, and reauthorization votes must be accompanied by clear metrics: how many investigations opened, how many violations found, and the fiscal cost per user affected. Strong oversight converts rhetorical promises of security into measurable, accountable practices.
Strategies for Advocacy in a Fear-driven World
Targeted, evidence-based campaigns beat broad alarmism. Use FOIA requests to build fact-backed narratives, fund strategic litigation that forces judicial review of overreach, and run local initiatives that adopt concrete privacy ordinances. Coalition-building across civil-rights groups, conservative fiscal watchdogs, and privacy-focused tech coalitions proved decisive in several 2010s fights; the bipartisan support that moved the USA FREEDOM Act is a model for future efforts that align with a Republican form of government’s emphasis on limited federal power.
Media strategy matters: supply reporters with verified data, timelines, and cost analyses so stories focus on measurable harms—budget overruns, error rates in predictive policing, and documented misuses of surveillance—rather than abstract threats. Training programs that teach the SIFT verification routine and basic digital hygiene in high schools and civic organizations scale resilience; communities that can evaluate claims independently are far less likely to accept fear-based policy grabs.
For immediate effect, organize town halls and voter guides that tie privacy and oversight to specific policy outcomes (e.g., votes for reauthorization, local procurement rules banning face recognition). Support candidates who pledge to defend individual liberties and sponsor legislation for mandatory audits and sunset clauses. Donating to legal defense funds, supporting state privacy ballot measures, and pressuring tech vendors during procurement can shift incentives away from fear-driven contracts and back toward accountable public service.
The Future of National Security
Advances in AI, biometric identification, and ubiquitous sensors mean the next decade will shift from manual surveillance to algorithmic mass monitoring—facial-recognition networks, predictive-risk scoring, and cross-agency data lakes that can link location, financial, and communications records in real time. Historical precedents matter: after 9/11 the Patriot Act (2001) enabled sweeping authorities; the Snowden disclosures (2013) exposed NSA bulk metadata programs; and the USA FREEDOM Act (2015) rolled back some bulk collection. Those policy cycles show a pattern: emergency expansion, public revelation, partial rollback, then new technology that resets the cycle.
Public trust will hinge on measurable outcomes rather than fear-driven narratives: how many plots were disrupted, how many prosecutions relied on the new tools, and at what civil-liberty cost. Expect lobbying by defense contractors and private surveillance firms to intensify—another thread in the playbook of manufactured fear—so voters and officials must demand clear metrics, sunset clauses, and audited impact assessments before permanent powers are granted.
Rethinking Security Policies
Targeted authorities with built-in expirations offer a concrete alternative to open-ended powers. Policies like Section 215’s expiration in 2015 and the subsequent USA FREEDOM adjustments demonstrate that sunset provisions and targeted warrants can curb abuse: replace bulk collection with court-approved, specific selectors tied to probable cause, and require semiannual public reports on how many cases produced actionable intelligence.
Redesigning procurement rules will reduce political incentives to inflate threats. Require cost-benefit analyses for major security programs, mandate independent audits by the Government Accountability Office (GAO) before multi-year contracts, and bar vendors from political consultancy roles while bidding. These steps address both the technical inefficiencies and the political economy that fuels fear-based policy expansions.
Balancing Safety with Civil Liberties
Secret court authorizations and bulk metadata programs exposed since 2013 underline the danger of unchecked surveillance: mass collection without case-by-case judicial review erodes constitutional protections. Shifting to individualized warrants, strong data-minimization rules, and statutory limits on retention time can preserve investigatory capability while protecting citizens’ privacy.
Independent oversight matters: empower inspectors general with unredacted access, require the Foreign Intelligence Surveillance Court to publish redacted summaries of key rulings, and create civilian review boards for domestic intelligence activities. Those mechanisms reduce secrecy-driven abuses and provide empirical checks—numbers on warrants issued, prosecutions achieved, and data retained—so policy debates rest on facts, not fear.
Would you accept surveillance that never expires? Implement mandatory breach reporting, civil remedies for misuse, and whistleblower protections tied to clear chain-of-command reporting; combine these with penalties—criminal and financial—against agencies or contractors that violate statute to create real deterrents against overreach.
A Call for Good Governance
Reasserting a Republican form of government means restoring limited, accountable institutions that protect both security and individual liberty. Reinforce congressional oversight by requiring classified briefings to be followed by public, redacted summaries; legislate routine GAO performance audits for major security programs; and require annual reviews with automatic sunsets unless affirmative reauthorization occurs.
Campaign incentives must change: prohibit the use of classified threat assessments in campaign advertising without corroborated, declassified evidence; enforce disclosure of vendor ties to political campaigns; and tighten procurement rules to prevent fear-driven boondoggles. Those reforms reduce the profit motive for fearmongering and re-align policy with voter interests.
Practical steps include mandating independent impact studies before approving new surveillance systems, publishing a public scorecard—number of officials disciplined, audits completed, and programs terminated—and enforcing cooling-off periods for officials who move into private security firms. These measures create transparent accountability, independent audits, and electoral responsibility so national security protects citizens rather than exploiting them.
To wrap up
To wrap up, manufactured fear corrodes liberty and empowers politicians who profit from panic. What began as legitimate security concerns now too often becomes a tool for expanding surveillance and centralizing authority; ask yourself, if you prefer a Republican form of government that prizes limited power and individual rights, do you want emergency measures that never expire? The pattern is clear: fear wins votes and normalizes permanent powers that outlive the threats used to justify them.
The remedy is to defend real security in ways that honor restraint: targeted responses to cyber threats, foreign rivals, and domestic extremism, paired with transparency, judicial oversight, and strict sunset clauses. Would you accept broad, open‑ended powers for the sake of a headline? If not, uphold Republican principles of limited government, rule of law, and personal liberty by insisting security policy protect citizens rather than political advantage.
FAQ
Q: What exactly is “manufactured fear,” and how does it shape national security decisions?
A: Manufactured fear is the deliberate amplification or invention of threats by political actors, media outlets, or interest groups to shift public opinion and justify policy shifts. It can turn temporary measures into permanent powers—mass surveillance, expanded search authorities, and open-ended emergency rules often start as short-term fixes after a crisis. If you discovered that many of those “emergencies” were overstated to win votes, would you still accept sweeping, long-lasting intrusions into private life? The Republican form of government—built on limited federal power, clear separation of powers, and strong protections for individual rights—offers institutional guards against such abuse: sunset clauses, stronger judicial review, and state-level checks that force accountability and narrow, evidence-based responses rather than fear-driven expansions of authority.
Q: Have national security claims actually eroded civil liberties, and who benefits?
A: Yes. Laws and programs justified by urgent security claims have expanded surveillance capacities, loosened warrant requirements, and normalized data collection often without proportional oversight. Those expansions disproportionately benefit political actors and bureaucratic institutions that gain budget, power, and control when the public is scared. If surveillance powers meant to be temporary remained in place after the initial threat faded, how much personal freedom would be left? A Republican form of government can push back by restoring limits on federal reach, insisting on transparency, reinstating strict warrant and probable-cause standards, and empowering states and courts to protect citizens—so security serves the people rather than serving the ambitions of officials.
Q: Are some national security threats exaggerated for political advantage, and how can we tell the difference between real and inflated risks?
A: Yes—threat inflation happens when uncertainty, partisan motives, and media incentives combine. Real risks exist (cyberattacks, hostile state actors, violent domestic extremism), but they are sometimes framed in maximalist terms to justify permanent funding increases or emergency powers. Ask yourself: if a claim of imminent catastrophe led to permanent policy changes, would you demand transparent evidence and independent review? A Republican form of government favors clear standards of proof, legislative oversight, and independent expert assessments before major powers are granted—ensuring resources target genuine vulnerabilities rather than political theater.
Q: How can policymakers protect national security without surrendering privacy and personal freedoms?
A: By designing narrowly tailored, time-limited authorities with strict oversight and clear remedies for abuse. Practical steps include sunset provisions on surveillance laws, mandatory public reporting and classified audits, higher warrants standards, protections for encryption and private-sector data, and criminal penalties for unauthorized spying. If officials had to publicly justify each intrusive tool under penalty of law, would fear-driven tools survive scrutiny? The Republican form of government reinforces these checks through constrained federal authority, empowered state remedies, and robust judicial review—balancing a strong defense posture with protection of individual liberty.
Q: What reforms should Republicans pursue to stop fear-mongering while keeping the nation secure?
A: Pursue reforms that restore accountability and focus on effective defense: repeal or revise open-ended emergency and surveillance authorities; require congressional approval and sunset dates for major security measures; create independent, bipartisan threat-assessment bodies with automatic audits; strengthen whistleblower protections and prosecutorial accountability; decentralize nonimportant federal powers to states; and prioritize investments in real, measurable defenses (cyber resilience, border security, intelligence modernization) rather than rhetorical campaigns. If leaders had to choose between expanding power and protecting your liberty, which would you trust to defend your family? A Republican form of government—favoring local control, limited federal reach, and constitutional safeguards—provides the institutional framework to keep the nation safe without making fear a permanent policy lever.