Many individuals and businesses are falling victim to the growing threat of cybersquatting, where malicious actors register domain names similar to trademarks, personal names, or company names with the intent to deceive, profit, or harm. This abusive practice can lead to identity theft, financial loss, and damage to one’s brand image. With 5,516 new cases filed in 2022 alone, the need to protect your online identity is more crucial than ever. Learn how to detect and take action against cybersquatting to safeguard your name and reputation online.
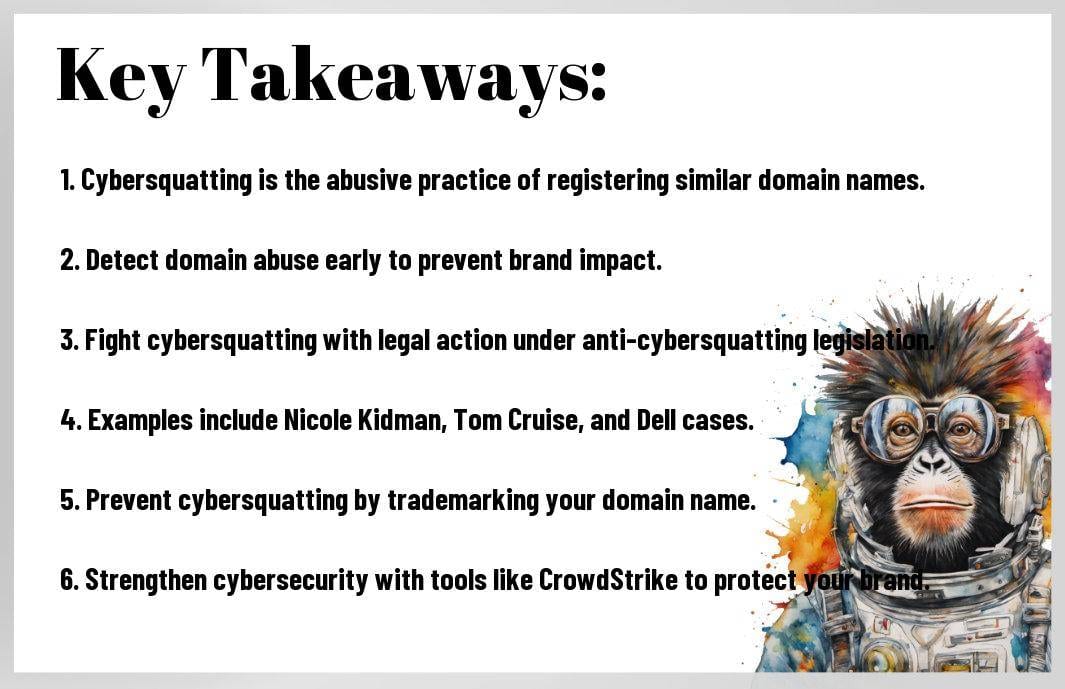
Key Takeaways:
- Cybersquatting Defined: Cybersquatting, typosquatting, or domain squatting is the abusive practice of registering and using internet domain names similar to trademarks for financial gain or malicious intent.
- Common Methods: Cybersquatting, typosquatting, and gripe sites are common methods used by bad actors to undermine digital investments and deceive users for profit or malicious activities.
- Detection and Prevention: Detecting domain abuse and taking action against cybersquatting is crucial to protect your company’s reputation and financial interests. Utilize digital risk protection tools and consider trademarking your domain name to prevent cybersquatting.
- Legal Action: Anti-cybersquatting legislation such as the ACPA and Lanham Act in the U.S., as well as ICANN arbitration, can help businesses combat cybersquatting through legal proceedings.
- Real-Life Cases: Examples of cybersquatting cases involving celebrities like Nicole Kidman and Tom Cruise, as well as corporations like Dell, highlight the importance of protecting brand identity in the digital age.
- Preventive Measures: Trademarking your domain name, registering different variations, and building up your cybersecurity posture with tools like CrowdStrike can help prevent cybersquatting and protect your online presence.
- Author Expertise: Bart Lenaerts-Bergmans, Senior Product Marketing Manager at CrowdStrike, brings over 20 years of experience in threat intelligence and cybersecurity, providing valuable insights on combating cybersquatting.
Understanding Cybersquatting
A growing concern in the digital world, cybersquatting is a malicious practice that involves registering domain names similar to those of established trademarks or personal names. These domains are then used for financial gain or illicit activities, such as delivering malware or stealing intellectual property. In 2022 alone, there were 5,516 new cases of cybersquatting reported, indicating a 10% increase from the previous year.
Types of Cybersquatting
- Cybersquatting: Involves registering domains of companies or individuals who have not secured their online presence yet, with the intention to sell them at a high price later.
- Typosquatting: Capitalizes on common typing errors by purchasing domains with slight misspellings of popular brand names, often used to launch malicious activities.
- Gripe Sites: Platforms dedicated to airing grievances about specific subjects, typically individuals, businesses, or products.
On the frontlines of cybersquatting defense, it is crucial for individuals and organizations to understand the nuances of each type of cybersquatting. Knowing the tactics used by bad actors can help in implementing proactive measures to protect online identities and intellectual property.
Typosquatting and Gripe Sites
Typosquatting takes advantage of human error by registering domains with slight variations from popular brand names, redirecting unsuspecting users to potentially harmful websites. In contrast, gripe sites serve as platforms for venting frustrations or criticisms about specific subjects. Both types pose significant risks to online security and brand reputation.
The rise of typosquatting and gripe sites underscores the importance of vigilance and proactive measures in safeguarding online identities and intellectual property. Understanding the tactics employed by cybercriminals and monitoring online activities are crucial steps in mitigating the risks posed by cybersquatting.
The Rise of Cybersquatting
Statistics and Examples
With the alarming rise of cybersquatting scams, statistics show that there were 5,516 new cases filed in 2022, representing a 10% increase from the previous year. This abusive practice of registering and using internet domain names to deceive users for financial gain or malicious intent is a growing concern in the digital landscape. One of the most well-known cases is the domain “whitehouse.com,” which redirects users away from the legitimate site to explicit content, showcasing the egregious misuse of domain names.
In addition to statistics, there are numerous examples of cybersquatting cases that have gone to court. For instance, movie star Nicole Kidman successfully took legal action against a typosquatting domain in 2001, highlighting the importance of protecting one’s online identity. Tom Cruise and Dell have also fought and won legal battles against cybersquatters, emphasizing the need for companies and individuals to safeguard their brand, name, and image in the digital age.
These statistics and cases underscore the growing threat of cybersquatting and the importance of taking proactive measures to prevent it, such as trademarking domain names and registering different variations to protect against malicious actors.
Notorious Cases of Cybersquatting
Notorious cases of cybersquatting, like those involving Nicole Kidman, Tom Cruise, and Dell, demonstrate the detrimental impact that this practice can have on individuals and businesses. For instance, Nicole Kidman’s legal victory against a typosquatting domain showcased the bad faith intent behind such actions and the need for legal recourse to protect one’s online identity. Companies like Dell have also taken strong legal action to safeguard their trademarks and reputation from being exploited by cybersquatters.
Notorious cases of cybersquatting serve as cautionary tales for individuals and businesses alike, highlighting the need for vigilance and proactive measures to prevent falling victim to such malicious practices that can result in financial losses and damage to brand reputation.
For instance, by leveraging cybersecurity solutions like CrowdStrike’s Digital Risk Protection tools and taking legal action under anti-cybersquatting legislation, companies and individuals can protect their online identities and assets from the growing threat of cybersquatting in today’s digital landscape.
How to Take Action Against Cybersquatting
Detecting Domain Abuse
For companies facing the threat of cybersquatting, detecting domain abuse is paramount. Detecting targeted domain abuse can be accomplished via digital risk protection tools or services. These offerings received newly domain registrations and can detect creating of look-a-like domains via specific algorithms. Newly registered domains are compared and if they match too close the user domain, alerts will be generated. It is important to detect the domain BEFORE the new site is fully operational so any brand impact, identity or data loss can be avoided.
Anti-Cybersquatting Legislation
To address cybersquatting effectively, anti-cybersquatting legislation plays a crucial role in protecting individuals and businesses. If you think you have a cybersquatting problem, it’s helpful to start with a bit of investigation. You can begin by searching the WHOIS database to identify the domain owner. From there, you can contact the owner to better understand their willingness to let go of the domain or to sell it at a price you consider reasonable.
Consulting with an attorney can help you determine if your case is supported by today’s anti-cybersquatting legislation. Some of these include: Anti-Cybersquatting Piracy Act (ACPA) which protects the intellectual property rights of trademark owners from cybersquatters, Lanham Act that helps protect trademarks of businesses and organizations, and Internet Corporation for Assigned Names and Numbers (ICANN) which helps resolve cybersquatting disputes by arbitrating issues about abusive domain name registrations.
Examples of Cybersquatting Cases that Went to Court
Understanding real-world examples of cybersquatting cases that have gone to court can shed light on the importance of taking action against such deceptive practices. Nicole Kidman, Tom Cruise, and Dell are just a few of the notable cases where individuals and companies took a stand against cybersquatters. In each case, legal action was necessary to protect their brand, name, and image from exploitation.
Preventing Cybersquatting
Trademarking Your Domain Name
For individuals and businesses looking to protect their online identity and prevent cybersquatting, one crucial step is to trademark your domain name. According to the 2024 Global Threat Report, cybersquatting scams are on the rise, making it necessary to take proactive measures. By trademarking your domain name, you gain a legal upper hand in cases of domain squatting, allowing you to take action against anyone attempting to register a similar domain for malicious purposes.
Trademarking your domain name provides you with a level of protection that can help safeguard your online presence and brand reputation. As demonstrated in cases like Nicole Kidman’s and Tom Cruise’s legal battles against cybersquatters, having a trademark in place can be a powerful tool in combating unauthorized use of your name or brand online.
Additionally, trademarking your domain name can act as a deterrent to potential cybersquatters, as they are less likely to target a name that is legally protected. Overall, this step is an necessary part of your cybersecurity strategy to defend against the growing threat of cybersquatting.
Registering Different Variations of Your Domain
To further safeguard your online identity and prevent cybersquatting, it is advisable to register different variations of your domain. While this may initially incur additional costs, it is a proactive measure that can save you from potential financial and reputational losses down the line. By securing various permutations of your domain, you create a defensive barrier against malicious actors looking to exploit similar domain names for fraudulent purposes.
Registering different variations of your domain also ensures that you maintain control over how your brand is represented online. This approach can help redirect traffic to your main domain and prevent cybersquatters from diverting visitors to unauthorized sites. By taking this preventive step, you fortify your cybersecurity posture and reduce the risk of falling victim to cybersquatting schemes.
Variations of your domain include misspellings, alternate extensions, and common typographical errors that cybersquatters may capitalize on. By proactively registering these variations, you establish a defensive perimeter around your online presence, making it harder for malicious actors to exploit your brand name for their gain.
The Importance of Cybersecurity
Building Up Your Cybersecurity Posture with CrowdStrike
Your online presence can be a target for cyber threats such as cybersquatting, which can lead to detrimental consequences for your brand and identity. Any proactive measures you take to enhance your cybersecurity posture are crucial in safeguarding your digital investments. By leveraging tools like Falcon Intelligence Recon and the Recon+ service from CrowdStrike, you can stay ahead of cyber criminals and prevent financial losses due to domain squatting.
With a complex cyber threat landscape dominating the digital realm, it is imperative to invest in leading cybersecurity solutions to protect your brand, data, and systems from malicious actors. CrowdStrike’s Digital Risk Protection tools offer comprehensive capabilities to combat threats like typosquatting and brand abuse effectively. The Recon+ team can provide actionable insights, evidence, and recommended strategies tailored to maximize efficiency in fighting domain misuse.
Protecting your online identity with robust cybersecurity measures is paramount in today’s digital age. As cybersquatting scams continue to rise, organizations and individuals must prioritize securing their online assets to prevent potential financial loss and reputation damage. CrowdStrike’s advanced cybersecurity solutions offer a proactive approach to defending against cyber threats, ensuring your brand, data, and systems are safeguarded from malicious activities.
Protecting Your Brand, Data, and Systems
Posture
Cybersecurity is at the forefront of safeguarding your brand, data, and systems from the pervasive threat of cybersquatting. The ability to detect and mitigate domain abuse before it impacts your online presence is crucial in maintaining a strong cybersecurity posture. Through proactive measures and utilizing digital risk protection tools, organizations can effectively combat the rising instances of domain misuse.
Real-Life Examples of Cybersquatting Cases
Nicole Kidman
Once again, the issue of cybersquatting reared its ugly head in the case of movie star Nicole Kidman. In 2001, Kidman took legal action against a website called NicholeKidman.com, which was a typosquatting domain aiming to capitalize on a slight spelling variation of the actress’s name. The WIPO Arbitration and Mediation Center ruled that the domain was being used in bad faith and should be transferred to Kidman’s ownership.
Cybersquatting can have severe repercussions for individuals, as seen in Nicole Kidman’s case. The deliberate misuse of domain names not only damages reputations but can also lead to financial losses and identity theft. This example highlights the importance of taking swift action against cybersquatting to protect the online identities of prominent personalities.
Furthermore, the legal battle fought by Nicole Kidman sheds light on the detrimental effects of cybersquatting and the necessity for individuals to safeguard their names and reputations in the digital landscape.
Tom Cruise
Nicole Kidman was not alone in facing the challenges of cybersquatting. In 2006, actor Tom Cruise also found himself entangled in a legal dispute with notorious cybersquatter Jeff Burgar. The WIPO panel ultimately ruled in favor of Tom Cruise, recognizing the actor’s rights to his name and the detrimental effects of domain misuse.
It is evident from Tom Cruise’s case that cybersquatting poses a significant threat to individuals with notable names. Taking proactive measures to prevent domain misuse and swiftly addressing instances of cybersquatting through legal means are crucial steps in protecting one’s online identity and reputation.
Nicole Kidman and Tom Cruise’s experiences serve as cautionary tales, emphasizing the importance of vigilance and action against cybersquatting to preserve personal and professional integrity in the digital realm.
Dell
Plus, the tech giant Dell faced its own battle against cybersquatting in 2007 when it took legal action against three website registrar firms for unlawfully profiting from domains similar to Dell’s trademarks. This successful lawsuit underscored Dell’s commitment to protecting its brand from being misused and misrepresented online.
Nicole Kidman and Tom Cruise may be household names, but even large corporations like Dell are not immune to the threats posed by cybersquatting. These cases highlight the pervasive nature of domain misuse and the critical need for organizations to actively defend their brands in the digital sphere.
Moreover, Dell’s legal victory exemplifies the importance of stringent measures and legal recourse in combating cybersquatting to safeguard brand integrity and customer trust.
To wrap up
To wrap up, the issue of cybersquatting poses a significant threat to individuals and businesses alike. The growing prevalence of this malicious practice demonstrates the importance of safeguarding online identities and brand reputations. By understanding the various forms of cybersquatting, such as typosquatting and gripe sites, individuals can better recognize and combat these deceptive tactics.
Moreover, taking proactive steps to prevent cybersquatting, such as trademarking domain names and registering variations, can help mitigate the risks associated with online identity theft. Leveraging cybersecurity solutions like CrowdStrike’s Digital Risk Protection tools can provide additional layers of defense against cybersquatting attempts and other cyber threats.
Overall, the fight against cybersquatting requires vigilance, awareness, and a strategic approach to protecting one’s digital presence. By staying informed and actively addressing potential threats, individuals and businesses can safeguard their online identities and maintain trust with customers in an increasingly digital world.
FAQ about “Cybersquatting Your Name: When Your Online Identity is Stolen”
Q: What is cybersquatting?
A: Cybersquatting is the abusive practice of registering and using an internet domain name that is identical or similar to trademarks, service marks, personal names, or company names with the bad faith intent of hijacking traffic for financial profit, delivering malware payloads, or stealing intellectual property.
Q: What are some examples of cybersquatting?
A: Examples of cybersquatting include registering domains like “whitehouse.com” to divert traffic away from legitimate sites, or typosquatting domains with slight spelling variations to trick users, like “rnarriott.com” or “yuube.com”.
Q: How can cybersquatting harm individuals or companies?
A: Cybersquatting can lead to customer turnover, identity theft, data loss, damage to brand image, and financial loss for individuals or companies.
Q: What are some measures to prevent cybersquatting?
A: To prevent cybersquatting, individuals or companies can trademark their domain name, register different variations of their domain, and invest in leading cybersecurity solutions to protect their online presence.
Q: What legal actions can be taken against cybersquatting?
A: Legal actions against cybersquatting may involve consulting with an attorney to understand anti-cybersquatting legislation like the Anti-Cybersquatting Piracy Act (ACPA) or the Lanham Act, which protect trademark owners from cybersquatters.
Q: How can organizations detect domain abuse?
A: Organizations can detect domain abuse through digital risk protection tools or services that monitor newly registered domains and detect lookalike domains that could be used for malicious purposes.
Q: What are some notable cybersquatting cases that went to court?
A: Notable cybersquatting cases include legal actions taken by celebrities like Nicole Kidman and Tom Cruise against individuals who registered domains using variations of their names in bad faith.